Robot vacuums are among the most popular smart home devices on the market, but their internet-connected cameras, microphones, and mapping systems have also raised new questions about robot vacuum security and privacy. Recent incidents involving DJI, Ecovacs, and Roomba have shown that smart robot vacuums can be vulnerable to hacking attempts, software flaws, and data privacy concerns.
In this article, we break down several real-world robot vacuum security incidents, explain how these smart home vulnerabilities happened, and outline practical steps users can take to better protect their robot vacuums and other connected devices.
How Smart Robot Vacuums Connect to the Internet
First, a little context. The Internet of Things, or IoT, is a network of physical objects embedded with sensors that exchange data over a network. This is what allows your robot vacuum to send app notifications, create maps, or start a cleaning task remotely.

Diagram showing how robot vacuums function as part of the Internet of Things (IoT), connecting with other smart home devices through a shared Wi-Fi network. © Vacuum Wars
Because robot vacuums are connected smart home devices, they face many of the same cybersecurity risks as smart cameras, smart TVs, and other internet-connected products. Any smart device in your home is, for all intents and purposes, a Wi-Fi-connected computer—and computers can be compromised.
There are several ways this can happen, and not all vulnerabilities work the same way.
The DJI Robot Vacuum Hack Explained
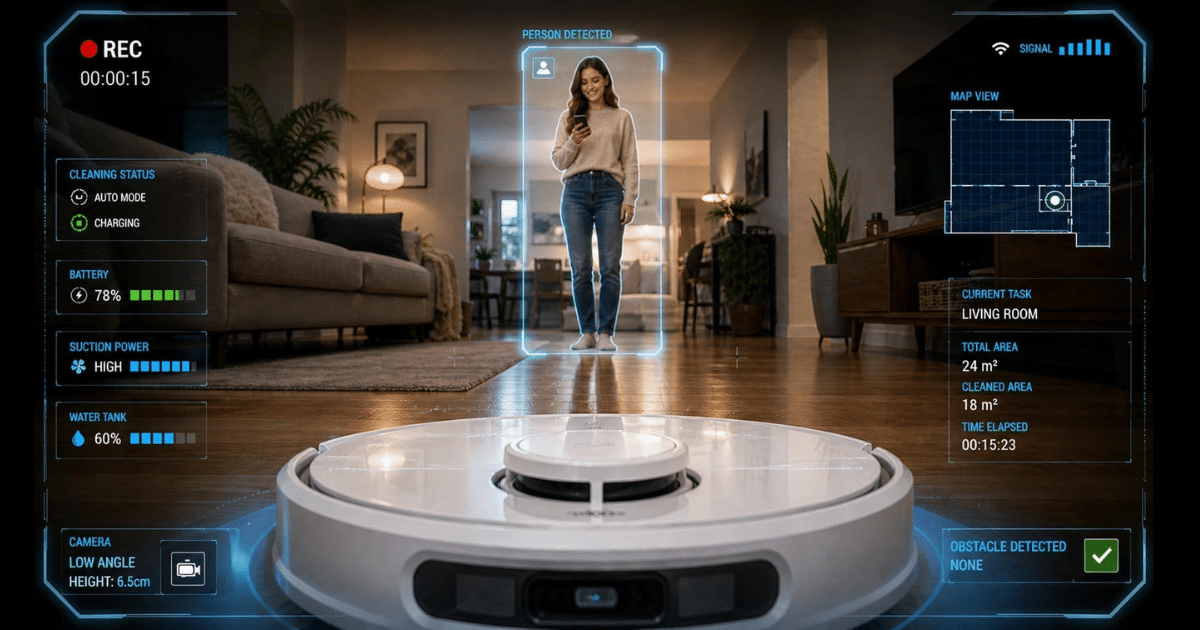
A software and AI professional named Sammy Azdofall wanted to hack his own DJI robot vacuum in order to drive it with a PS5 controller. To pull it off, he used an AI coding tool to dig into the robot software, and what he found revealed a major robot vacuum security vulnerability.
The app was supposed to give each user a private key to access their own device. But when he used his key on DJI’s servers, it unlocked not just his robot, but thousands of others.
In total, around 10,000 DJI devices were exposed. He was reportedly able to access maps, look through cameras, and remotely control affected robot vacuums. He quickly sounded the alarm, and the vulnerability has reportedly since been patched.
IBM’s X-Force cybersecurity team has warned that AI-assisted coding and analysis tools are increasingly being used to identify software weaknesses like these. Since no software is completely bulletproof, vulnerabilities in smart home devices may continue to emerge as connected products become more advanced.
The flaw reportedly existed in the identity architecture of the robot’s backend system when the server failed to properly restrict user access permissions. In simple terms, while the access code proved Azdofall was a legitimate DJI customer, the server failed to bind his account to only his own robot vacuum.
As a result, one user credential effectively became a master key for thousands of devices. It was a serious smart home security failure that fortunately came to light through someone experimenting on his own device rather than through malicious attackers.
See also: DJI Romo Robot Vacuum Security Flaw Allowed Remote Camera and Data Access
The Ecovacs Robot Vacuum Security Breach
The Ecovacs incident in 2024 was a very different kind of robot vacuum hack.
Users in different parts of the U.S. reported that their robot vacuums started spontaneously moving around their homes, shouting slurs, and even chasing a dog. One user quickly changed the password on the device, but it didn’t help. The attackers had effectively gained remote control of the robot vacuum.
The hackers reportedly found a way to bypass the PIN entry system entirely without ever actually knowing the PIN itself.
Here’s why that worked: the robot vacuum itself never directly verified the PIN. Instead, it simply asked the app whether the PIN had already been entered. Attackers were allegedly able to trick the app into confirming authentication.

Once they did that, they gained deep-level access to the robot vacuum—not just the camera and microphone, but control over the entire machine. Because the vulnerability existed deep within the software architecture, changing passwords alone would not have prevented the intrusion.
Importantly, this was not caused by user error. It was a flaw built into the software itself. Firmware patches are critical for fixing these kinds of robot vacuum security vulnerabilities, and Ecovacs issued a firmware update in November 2024 to address the issue.
See also: Ecovacs Robot Vacuum Security Vulnerabilities Uncovered
The Roomba Privacy Leak and Why It Was Different
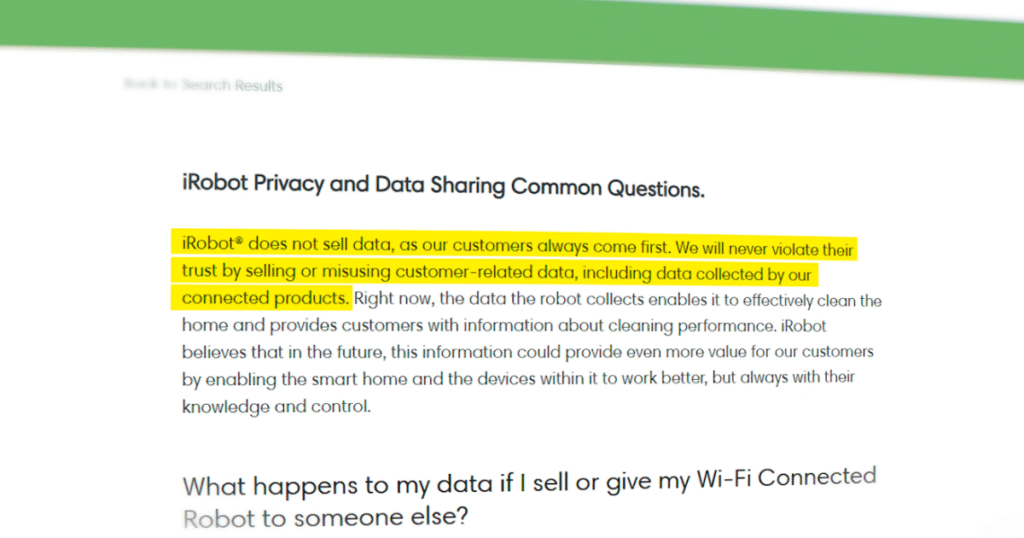
While the DJI and Ecovacs stories involved software vulnerabilities, the iRobot incident from a few years earlier centered more on robot vacuum privacy and data handling than hacking.
To train AI systems to recognize household objects, humans often need to review and label captured images. In 2020, development versions of the Roomba j7 series were reportedly capturing images and sending them to a third-party data-labeling company.
The privacy controversy emerged when workers took screenshots of sensitive images—including a woman sitting on a toilet—and shared them in private Facebook and Discord groups.
However, these were not normal consumer robot vacuums. They were development devices distributed to paid testers and employees who had signed agreements acknowledging that image collection was taking place. Some units reportedly even displayed stickers indicating that video recording was active.
While the testers technically consented to the data collection, they clearly did not consent to sensitive images being shared by workers hired to process the data.
iRobot responded by terminating its relationship with the service provider and tightening its data governance policies. Since then, the company has moved further toward edge AI processing, where image recognition happens directly on the robot vacuum itself rather than being processed remotely in the cloud.
iRobot later received recognition from organizations including Consumer Reports and the Mozilla Foundation for improvements in privacy and smart home security practices.
See also: Are Robot Vacuums Spying on You? A Deep Dive into Privacy & Security Risks
Why Smart Home Devices Are Frequent Targets
The biggest smart home cybersecurity risks are often less dramatic than viral hacking stories—but far more common.
According to a report from Netgear and Bitdefender, the average smart home experiences 29 cyberattack attempts per day. These are generally not targeted attacks aimed at specific individuals. Instead, they are highly automated systems constantly scanning the internet for vulnerable smart home devices with weak passwords or outdated firmware.
Smart TVs are reportedly among the most frequently targeted devices, highlighting that this is a broader smart home security issue rather than something unique to robot vacuums.
The goal is often to quietly recruit compromised devices into larger botnets used for cybercrime, hiding internet traffic, or even cryptocurrency mining—all without the owner realizing it.
According to the report, 93% of these attacks are fully automated. In most cases, there is no individual hacker specifically targeting your robot vacuum. Instead, automated software continuously probes internet-connected devices looking for easy points of entry.
How to Protect Your Robot Vacuum From Hackers
Fortunately, there are several practical robot vacuum security tips that apply to almost any smart home device.
Use Strong Passwords
First—and most importantly—never use default usernames or passwords. Automated bots constantly scan internet-connected devices for weak credentials such as “1234” or reused passwords from previous data breaches.
IBM’s X-Force team recommends using long, complex passwords and never reusing them across multiple accounts.
Set Up a Guest Network
Another strong smart home security practice is creating a guest Wi-Fi network specifically for smart devices like robot vacuums, smart TVs, and cameras.
This separates connected devices from more sensitive systems like your personal computer or smartphone. Even if one smart device becomes compromised, it becomes harder for attackers to access the rest of your network.
One important note: many robot vacuums only connect to 2.4 GHz Wi-Fi networks, so your guest network should support that frequency.
Keep Firmware Updated
Firmware updates are one of the most important ways manufacturers patch known robot vacuum security vulnerabilities.
This is exactly how Ecovacs addressed its PIN bypass issue. Keeping your robot vacuum firmware current helps maintain both security and software stability.
Disable Features You Don’t Use
Another good cybersecurity practice is minimizing your “surface area of vulnerability.” If your robot vacuum includes features like remote camera viewing or voice controls that you never use, disabling them reduces unnecessary exposure.
Final Thoughts on Robot Vacuum Security
Robot vacuums and other smart home devices can genuinely make home maintenance easier, and we use them ourselves regularly. But there are real trade-offs involved whenever you introduce an internet-connected device with cameras, microphones, and mapping capabilities into your home.
The good news is that most robot vacuum security risks can be reduced significantly through strong passwords, firmware updates, network segmentation, and careful management of device permissions.
As smart home technology continues to evolve, understanding both the benefits and the risks of connected devices will become increasingly important for consumers.
Frequently Asked Questions
Can robot vacuums be hacked?
Yes. Like other smart home devices, robot vacuums can potentially be hacked through software vulnerabilities, weak passwords, or outdated firmware.
Are robot vacuum cameras secure?
Most modern robot vacuum manufacturers use encryption and firmware updates to improve security, but privacy risks can still exist depending on how image data is processed and stored.
How do I make my robot vacuum more secure?
Use strong passwords, keep firmware updated, place smart devices on a guest network, and disable features you do not use.
Was the Roomba privacy leak a hack?
No. The Roomba incident involved development devices and data-labeling workers sharing sensitive images rather than hackers breaking into consumer robot vacuums.
Why do robot vacuums need internet access?
Robot vacuums use internet connectivity for app controls, mapping updates, firmware updates, remote monitoring, and smart home integrations.
Top 20 Robot Vacuums
Explore Vacuum Wars’ always up-to-date rankings of the best robot vacuums, based on independent, hands-on testing. We purchase every unit ourselves and have evaluated more than 150 models, giving us a deep benchmark for cleaning performance, navigation, battery life, and advanced features like obstacle avoidance and mopping.